This document describes the capabilities and configuration of the WAFXtender Managed Rules for AWS WAF. Subscription and pricing information is available in the listing in the AWS Marketplace.
Overview
ThreatSTOP’s WAFXtender is a collection of managed rules for AWS WAF. Each ruleset can be added to the configuration of one or multiple WAF. The rulesets extend the network protection by maintaining IP sets that will block malicious or unwanted incoming connections to web applications served using an AWS Elastic Load Balancer (ELB), API Gateway or CloudFront instance.
Rulesets are updated automatically throughout the day, as ThreatSTOP updates its database of malicious IP addresses and Threat Intelligence.
Four rulesets are available to customize your policy:
- Core Threats, to block HTTP specific threats and forum comment spamming bots
- Spiders/Crawlers, to block web spiders and crawlers
- Inbound HTTP Attacks, to block Anonymizing services such as TOR and VPNs.
- ITAR/OFAC, to block connections from networks mapped to countries listed by ITAR regulations or on the OFAC sanction list.
Rulesets are available as a subscription via the AWS Marketplace and can be added or removed from a WAF at anytime. Each ruleset is available independently.
Features
- Four rulesets that can be combined or selected individually.
- Rulesets block incoming connections from the IP subnets to the ELB, API Gateway or Cloudfront instances that the WAF is attached too.
- Rulesets can be added to the ACLs of one or multiple AWS WAFs. Subscriptions costs are incurred for each per WAF instance.
- Rulesets can be configured to block or only monitor (log) connections.
- Rulesets are updated multiple times daily.
Subscriptions
- Subscriptions can be started or ended at anytime. Note that terminating the marketplace subscription does not rem ove the already configured rulesets and costs will accrue until the rulesets are deleted from each WAF instance.
- Each ruleset is priced independently from the others.
- Subscriptions costs accrue for each per WAF instance. There is no additional costs if a WAF is assigned to multiple ELB instances.
- The subscriptions costs are separate from the usage costs for the Web ACL instances.
Terms of Service
The ThreatSTOP WAFXtender is licensed under the AWS Standardized License Terms.
Ruleset sizes and WCU Cost
The size of each rulesets depends on the number of IPs categorized by ThreatSTOP. The maximum sizes are as follows:
| Ruleset | Max number of IP subnets | WAF WCU |
|---|---|---|
| Core Threats | 100,000 | 10 |
| Spiders/Crawlers | 20,000 | 2 |
| Inbound HTTP Attacks | 20,000 | 2 |
| ITAR/OFAC | 50,000 | 5 |
Comparison with ThreatSTOP devices
WAFXtender is available via the AWS Marketplace without requiring a ThreatSTOP account, limiting the customization available. With a ThreatSTOP account, additional features become available.
The full version of the ThreatSTOP product lines provide many additional security 0features, with several hundreds types of Threats being tracked and available in customizable policies than can be loaded not only on an AWS WAF but also on many firewalls and DNS Servers (see the supported devices).
The main differences between the two options are listed in the table below.
| Feature | WAFXtender | ThreatSTOP Devices |
|---|---|---|
| AWS Account required | Yes | Yes (for WAF integration only) |
| No ThreatSTOP Account | Yes | No |
| Custom Rulesets | No | Yes |
| Custom IP addresses | No | Yes |
| Logging | Yes | Yes |
| Integrated Reporting | No | Yes |
| Cost | Usage based, hourly | Per-device per year |
Configuration
Managed Rules can be added during the creation of the Web ACL (in the Add rules and rule groups step) or added to an existing Web ACL by editing the Web ACL and selected the Rules tab. The Web ACL must be associated with an AWS Resource (an ELB instance, API Gateway or CloudFront instance)
Adding a ruleset
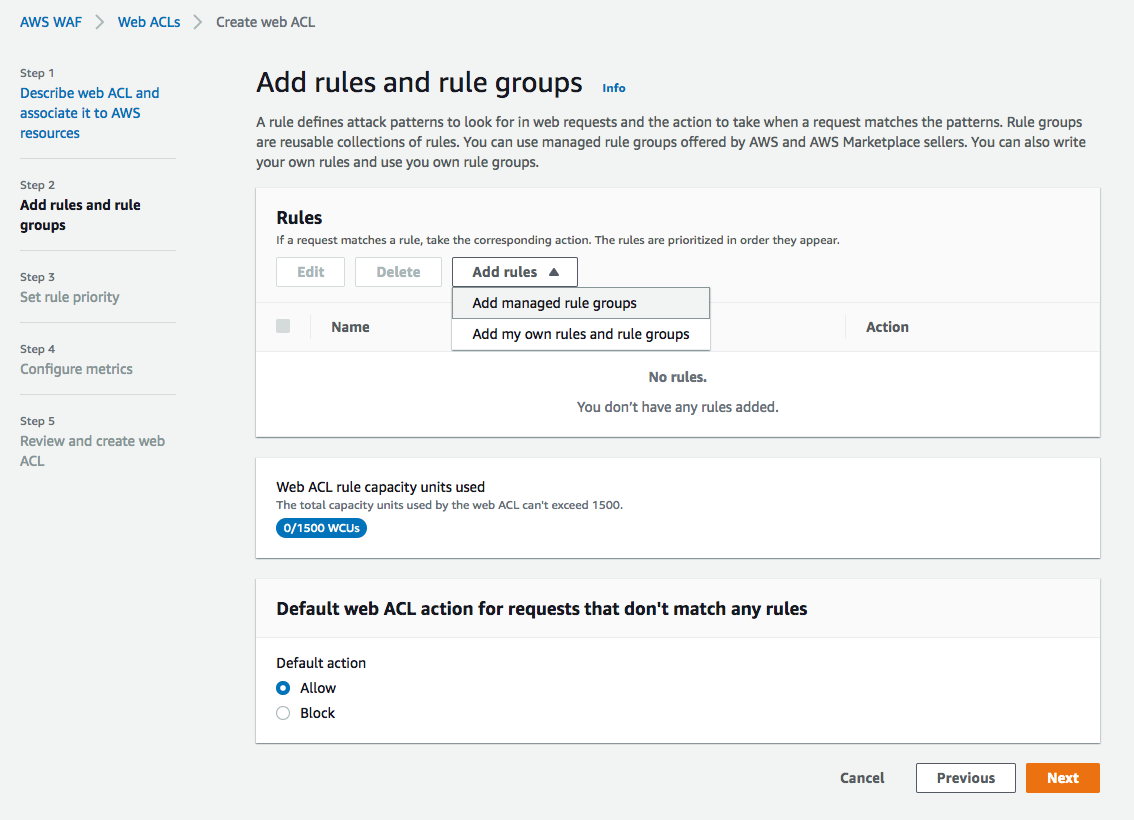
- When prompted to select rules, select the Add rules menu then the Add managed rule groups option.
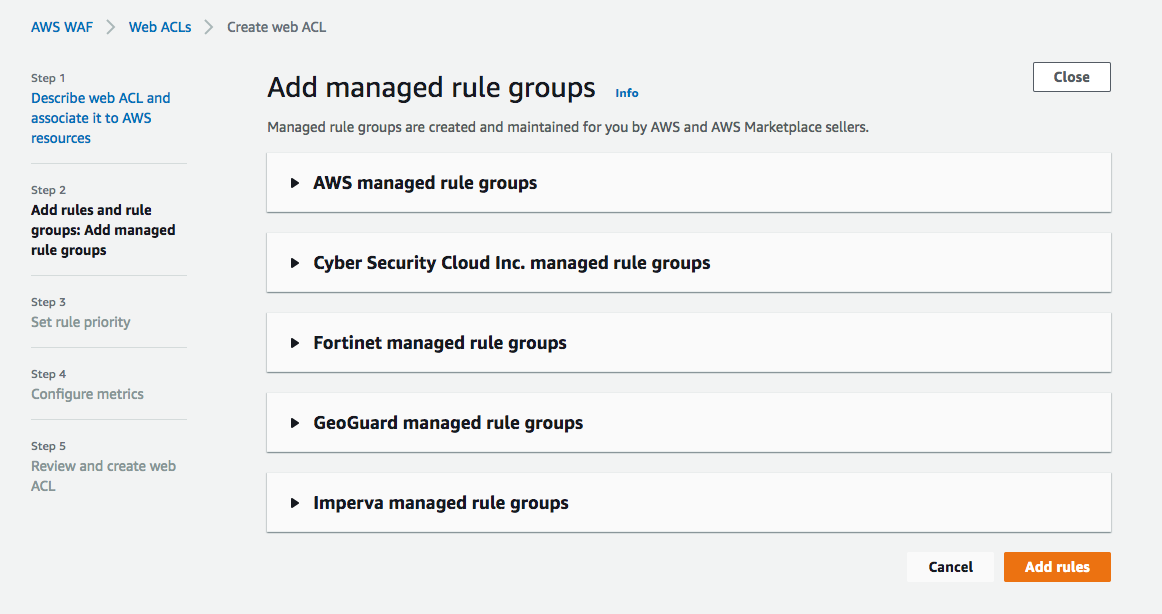
- You will be presented with a list of managed rules vendors - select the ThreatSTOP managed rule groups.
- If you have not already subscribed to the ThreatSTOP Managed Rules, you will need to do it now: click on the Subscribe in AWS Marketplace link
- the AWS Marketplace listing will open in a new tab.
- after reviewing the listing, proceed by clicking Continue to Subscribe.
- On the confirmation page, click Subscribe.
- Back to the Managed Rule selection, you can select any number of the ThreatSTOP rulesets by clicking Add to web ACL on the corresponding entries.
- After adding a ruleset, an option will appear to Set the rules action to count. If left unchecked, connections originating from the IP addresses in the ruleset will be blocked. If checked, they will only be logged (see Logging below).
- On the next page, set the priority of the rulset if you have use multiple sets.
Removing a ruleset
The ThreatSTOP WAFXtender rulesets can be removed from the Web ACL by editing the ACL, selecting the Rules tab and selecting the rules. This needs to be repeated for each WebACL that uses managed rulesets.
You can also end the subscription on the marketplace by visiting the subscription management page. Find the ThreatSTOP subscription, select Manage and Cancel Subscription in the Actions menu.
Please note that cancelling the subscription doesn’t remove the rulesets already applied to your Web ACLs instance.
Logging
A WAF instance can be configured to log connections blocked by its rulesets. Logging is enabled on the Logging and Metrics tab of the Web ACL configuration page.
Logging is configured using an AWS Kinesis Data Firehose, which will stream events into a selection of datastores.
An example of the logging configuration using AWS S3 is shown in the documentation of ThreatSTOP’s Custom WAF integration. The full integration includes a log parsing and reporting feature that will match hits generated by the rulesets against ThreatSTOP’s Threat Intelligence database. This feature is not available in the marketplace feature.
Support
If you have any questions or would like assistance to set up ThreatSTOP’s WAFXtender, please reach our Customer Support team at support@threatstop.com.
FAQ
WAF version
AWS introduced a new version of its WAF product, version 2. These rulesets are limited to v2 support and are not available for WAF Classic.
IP versions
The rulesets contain IPv4 addresses only and no IPv6 addresses.
References
- Getting Started with AWS WAF
- WAF Pricing information
- AWS WAF FAQ with a section about Managed Rules
- In depth video about Managed Rules including a demo of the configuration at 12:00